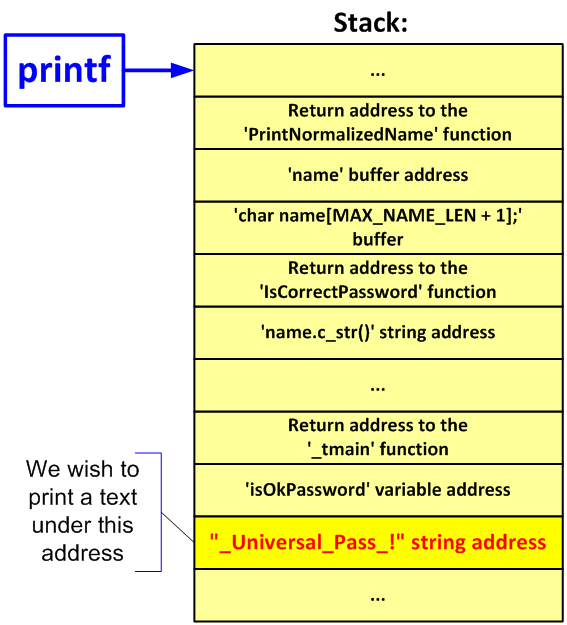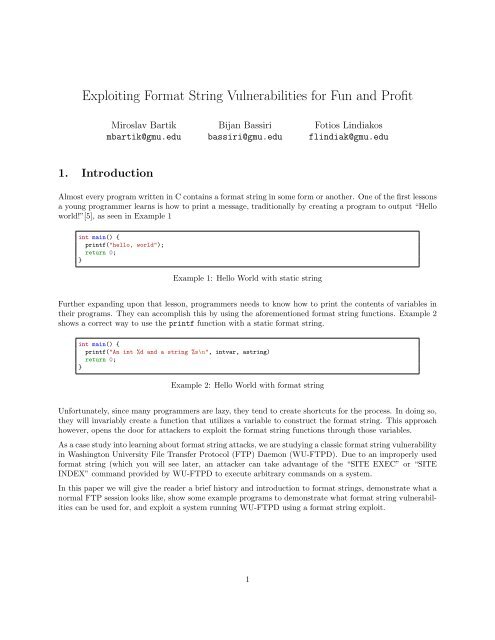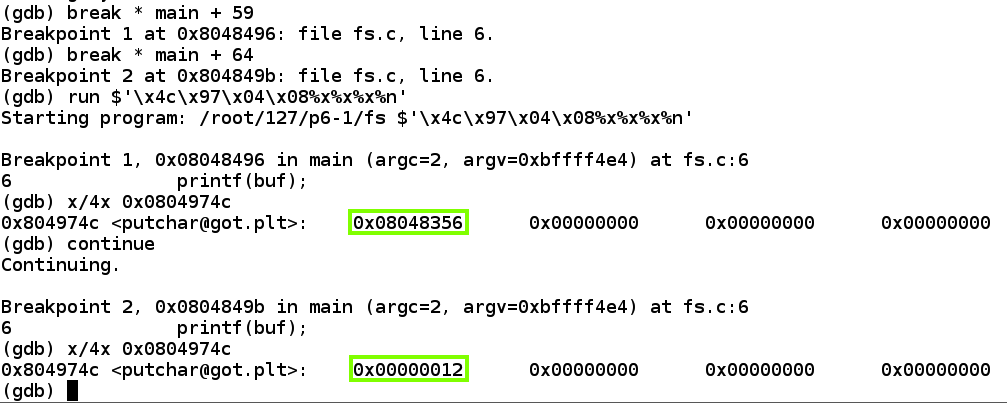
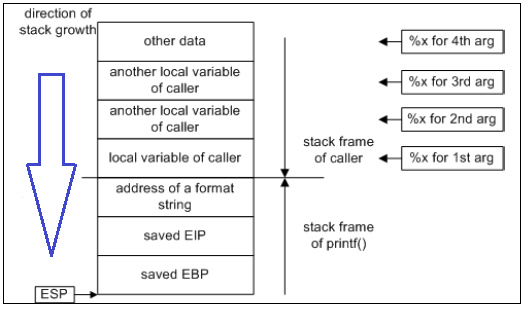
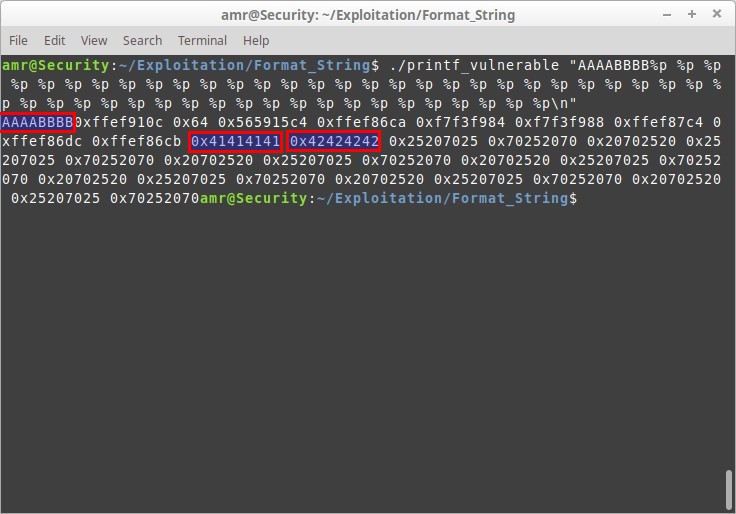
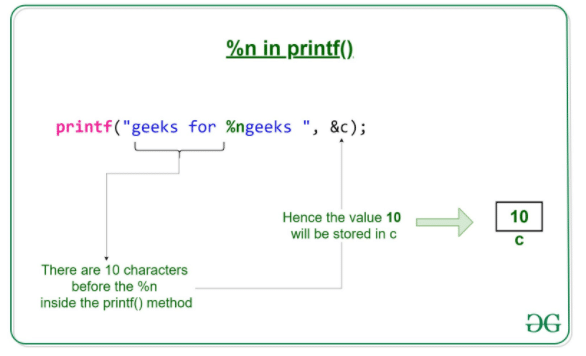
Exploit Development: How to Write Specific Values to Memory with Format String Exploitation « Null Byte :: WonderHowTo
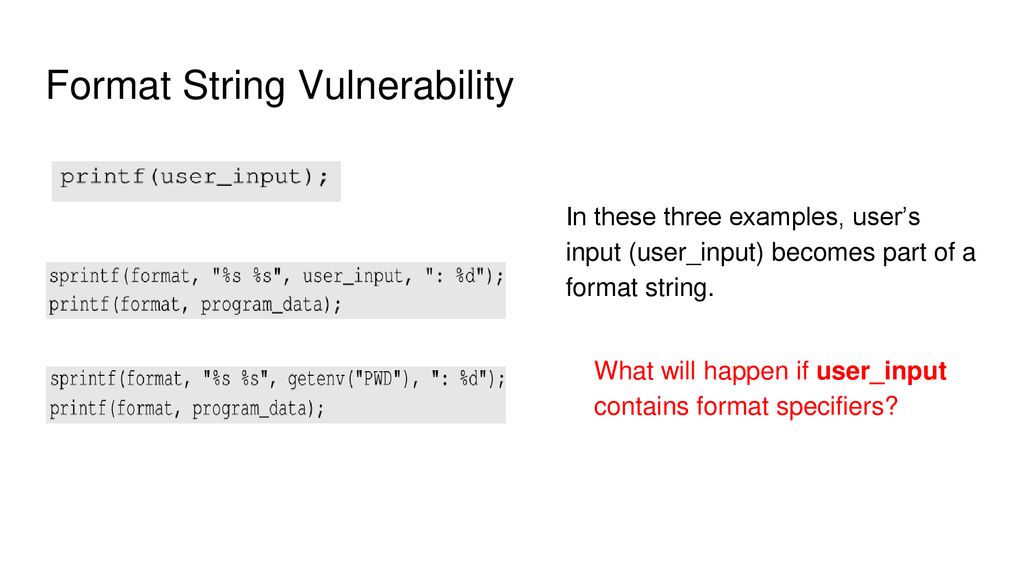
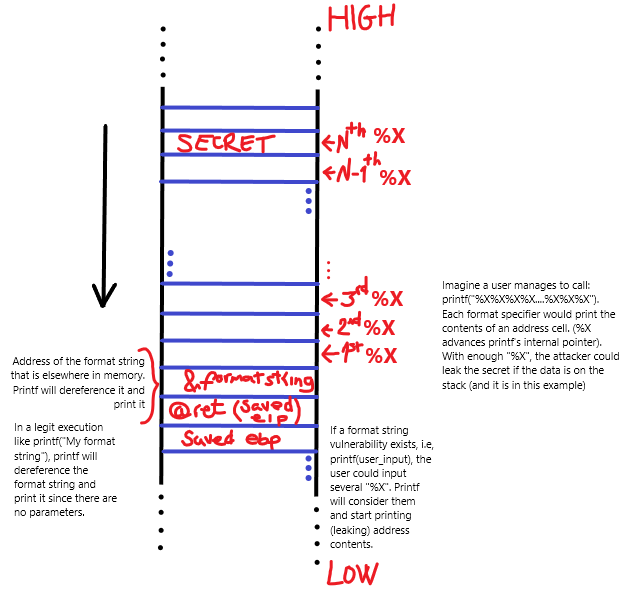
Security-Oriented C Tutorial 0x14 - Format String Vulnerability Part I: Buffer Overflow's Nasty Little Brother « Null Byte :: WonderHowTo


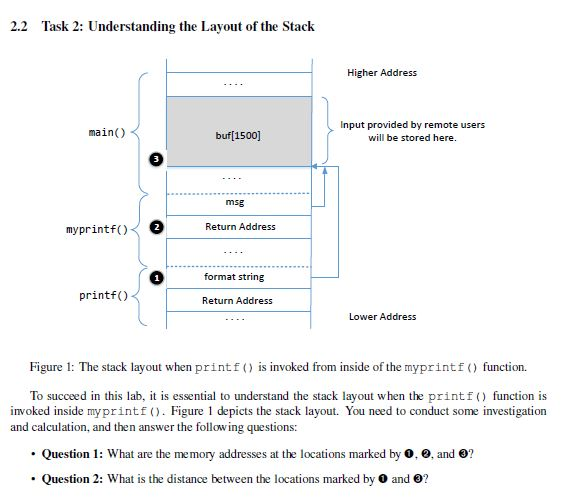
![ExpDev] Exploit Exercise | Protostar | Format 3 | by bigb0ss | InfoSec Write-ups ExpDev] Exploit Exercise | Protostar | Format 3 | by bigb0ss | InfoSec Write-ups](https://miro.medium.com/v2/resize:fit:1400/1*zA2gCGumIVo5nXY-Cvf26Q.png)